Unlock Efficiency and Control with Fulcrum
FulcrumTechnologies, Inc
Streamline Your Operations with Our Advanced Software Solutions
Discover the Power of Fulcrum Technologies
With over 25 years of experience in the industry, Fulcrum Technologies is a trusted name in software development and implementation. Our expertise spans various domains, including Asset Lifecycle Management, Inventory Management, Warehouse Management, GIS Tracking, Document Management, Regulatory Compliance, and more.
Companies Who Have Come for Fulcrum Powered Software Solutions


















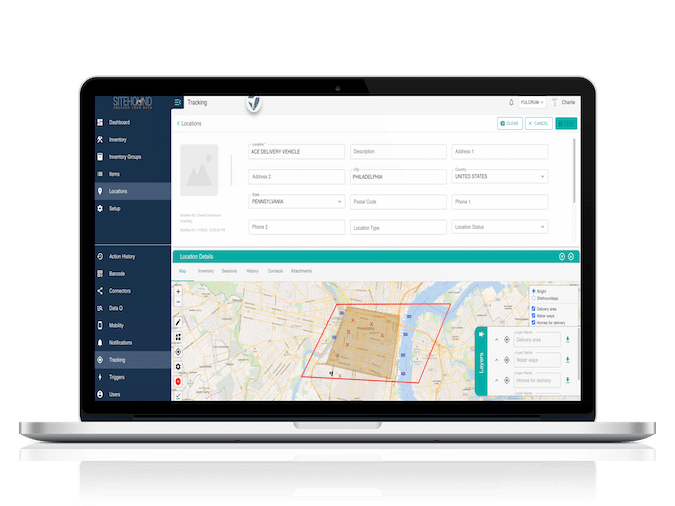
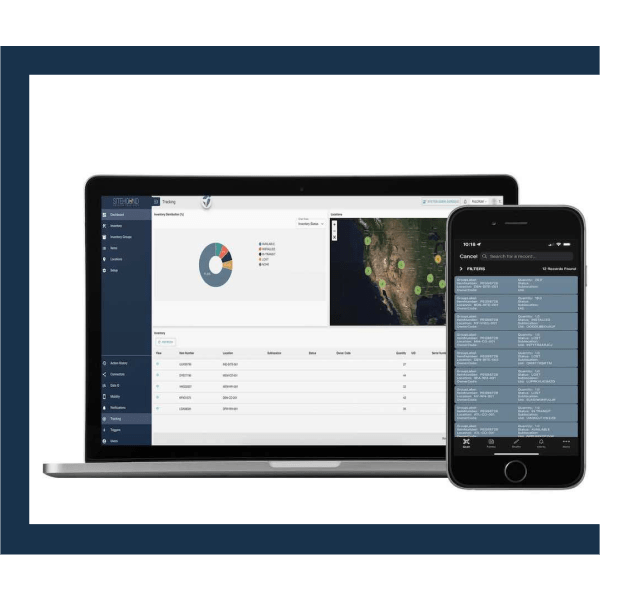
Optimize Asset Tracking
and Management with Sitehound
Say goodbye to manual tracking processes and embrace the efficiency of Sitehound. Our state-of-the-art asset tracking and management solution ensures real-time visibility into your valuable assets. Track assets effortlessly and streamline maintenance processes, enabling you to maximize productivity and minimize costs.

Seamless Communication
ePoll enables seamless communication between different software systems within your organization. Eliminate data silos, reduce manual effort, and enhance overall operational efficiency. With ePoll at your disposal, say goodbye to time-consuming data entry tasks and focus on what truly matters – growing your business.

INTEGRATION ENGINE
Powerful Integration Engine for Enhanced Workflow
Fulcrum’s integration engine acts as a central hub for connecting all your software applications effortlessly. Whether you need to sync data across multiple platforms or automate workflows between different systems, our integration engine simplifies the process, ensuring that information flows seamlessly through your organization.

Mapping & GIS
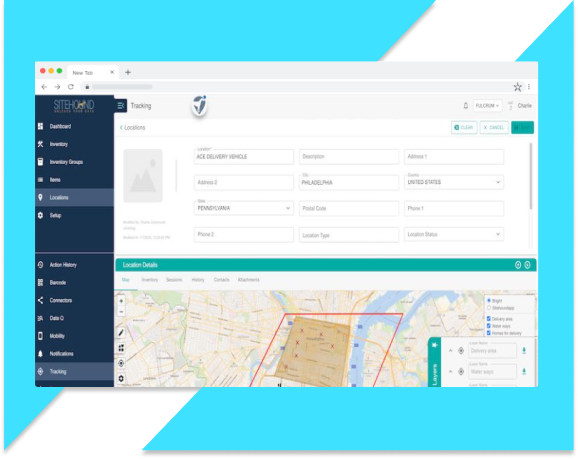
Unlock the Power of Location Intelligence
Navigate complex spatial data with ease using Fulcrum’s mapping & GIS solutions. Visualize geospatial information effectively and make informed decisions based on location intelligence. Transform raw data into actionable insights that drive business growth.
SERVICES
Let Fulcrum’s 25 years of experience help guide your inventory management strategy

Data Services
Say goodbye to cumbersome manual processes and hello to automated workflows. With Fulcrum’s Data Services, you can effortlessly extract data from various sources, transform it into a structure that suits your needs, and load it seamlessly onto your desired destination. Our platform empowers you to take control of your data and make informed decisions based on accurate insights.
Scale your data operations effortlessly with our flexible and scalable infrastructure. As your business grows, so does the demand for robust data capabilities. Our platform ensures that you can handle large volumes of data without compromising performance or reliability. Focus on driving strategic initiatives while we handle the heavy lifting in the background.
Unlock the true potential of your data with Sitehound’s Data Services Platform. Your journey toward real-time analytics and machine learning starts right here. Join countless satisfied customers who have already experienced the difference our platform brings to their data operations.
Software Training
Fulcrum’s support team is here to ensure you receive comprehensive training for all our software solutions. We offer a range of training options, including train the trainer, remote training, onsite training, and in-app guided training. Our experienced team is dedicated to providing you with the knowledge and skills you need to maximize the benefit of our enterprise-powered technology. Partner with Fulcrum Technologies for reliable software training that is both cost-effective and efficient.

Scanning Hardware
Looking to meet your scanning hardware needs? Look no further than Fulcrum Technologies. As the experts in enterprise power at a small business price, we have the solutions you need to streamline your asset tracking and management. With our top-of-the-line scanning hardware, you can efficiently scan and track your assets with ease. Whether you need barcode scanners, document scanners, or any other scanning equipment, Fulcrum Technologies has got you covered. Trust us to provide you with the reliable and high-quality scanning hardware you need to optimize your business operations. Contact us today to learn more about our scanning hardware options and how we can help you achieve maximum efficiency.
Barcode Labels
Providing custom barcode labels for any need, anywhere in the world. Fulcrum Technologies offers a wide range of barcode labels tailored to meet your unique requirements. Our enterprise power combined with small business pricing ensures cost-effective solutions for asset tracking and management. With our advanced TechnologySitehoundEpollIntegration EngineMappingGISServicesData ServicesSoftware TrainingScanning Hardware, we guarantee convenience and efficiency. Trust Fulcrum Technologies to deliver high-quality barcode labels that empower your business globally. Explore our resources, blog, newsroom, and FAQs, and contact us today for all your barcode labeling needs.